Draft
Conversation
Contributor
Author
|
S2V has been implemented 🎉 Need to add tests next |
83f303e to
760d327
Compare
This file contains hidden or bidirectional Unicode text that may be interpreted or compiled differently than what appears below. To review, open the file in an editor that reveals hidden Unicode characters.
Learn more about bidirectional Unicode characters
Sign up for free
to join this conversation on GitHub.
Already have an account?
Sign in to comment
Add this suggestion to a batch that can be applied as a single commit.This suggestion is invalid because no changes were made to the code.Suggestions cannot be applied while the pull request is closed.Suggestions cannot be applied while viewing a subset of changes.Only one suggestion per line can be applied in a batch.Add this suggestion to a batch that can be applied as a single commit.Applying suggestions on deleted lines is not supported.You must change the existing code in this line in order to create a valid suggestion.Outdated suggestions cannot be applied.This suggestion has been applied or marked resolved.Suggestions cannot be applied from pending reviews.Suggestions cannot be applied on multi-line comments.Suggestions cannot be applied while the pull request is queued to merge.Suggestion cannot be applied right now. Please check back later.
Feature Request: Decrypt Wasm Messages (Draft)
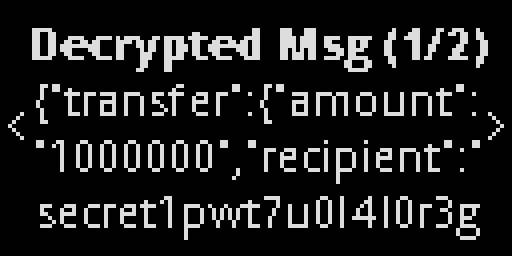
This PR introduces the ability for the Ledger app to decrypt the message being sent to Secret WASM contracts, allowing users to see the actual message contents they are signing (e.g., details of SNIP transfers) instead of the base64-encoded buffer of the encrypted message.
How it works
A new instruction code
0x42 #SIGN_SECP256K1_DECRYPTis introduced in order to remain backwards-compatible. The new instruction allows callers to include an optional AES-128-SIV key (the transaction encryption key) which was used to encrypt the WASM message (see docs preview here).The app then performs all the same checks and parsing as it does with
0x02 #SIGN_SECP256K1, in addition to verifying authenticity/integrity of the encrypted data via CMAC.When displaying pages to the users, the app replaces the encrypted base64-encoded string with the decrypted message contents, allowing for transparent signing.
This approach ensures that the app is still signing the exact same payload as before, and that a malicious caller would not be able to trick users into signing a different message (e.g., by providing a false decryption key).
A note on app size
This implementation makes use of system libraries and already imported libs wherever possible, maintaining as small a footprint as possible to cut down on app size. v2.34.1 of the Secret app for Nano S is currently 46 KB (1/3rd the capacity of the device). Upon reviewing the entire source code, I believe there is a fair amount of optimization that can be done to reduce this size. A follow-up item will be to attempt to apply these optimizations.
Steps remaining before PR is moved out of draft status: